Overview
Your Outlook can change everything

Take the tour
See Outlook in Action
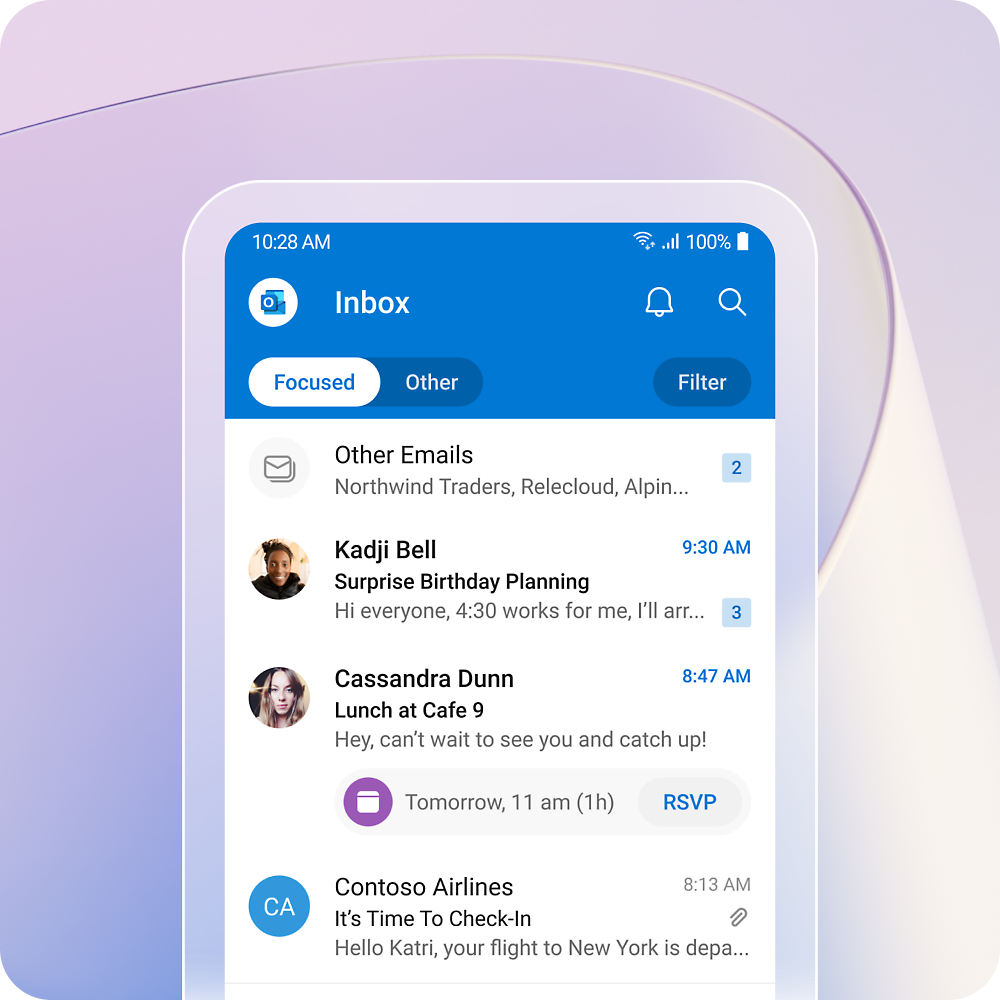
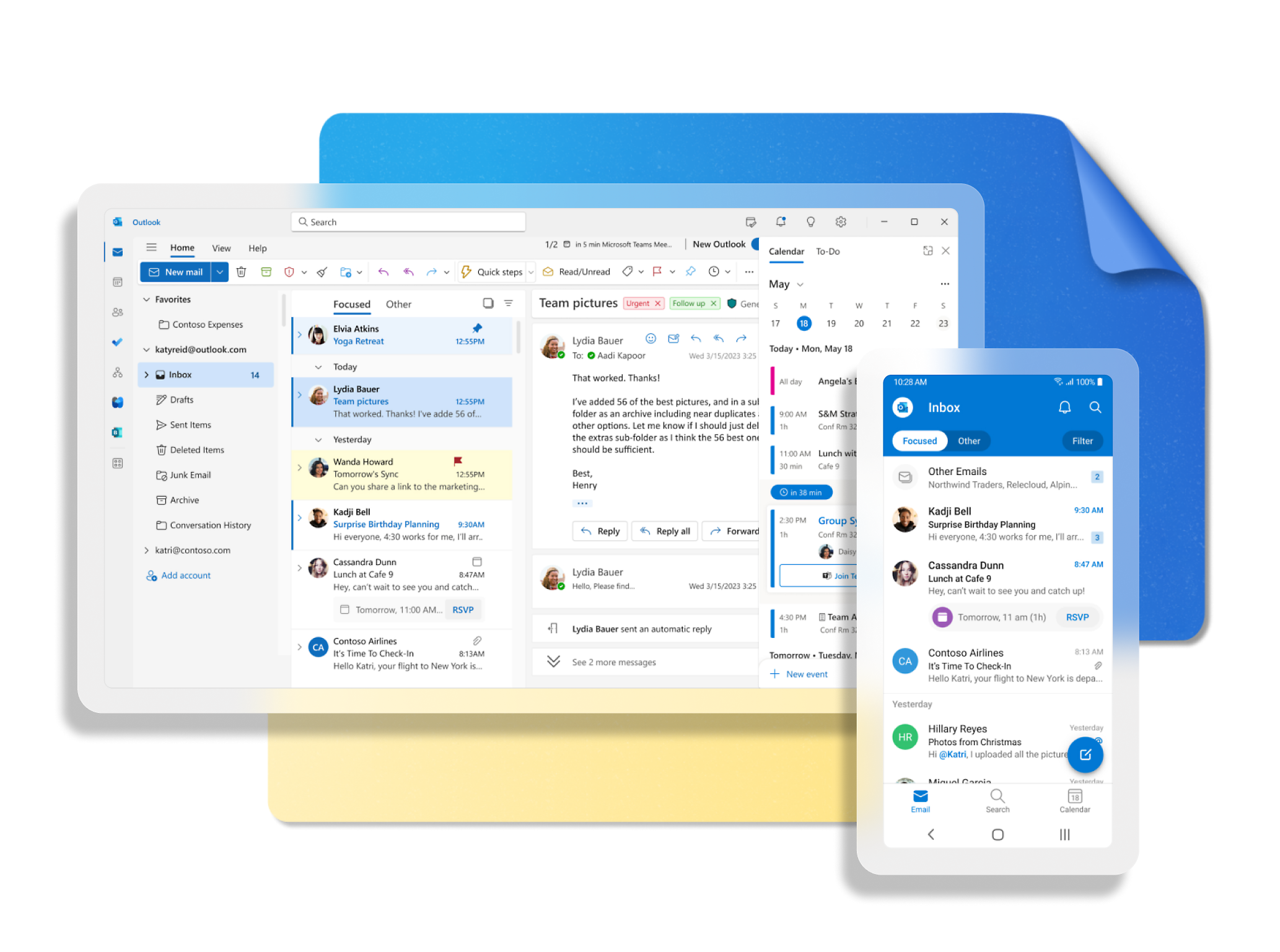
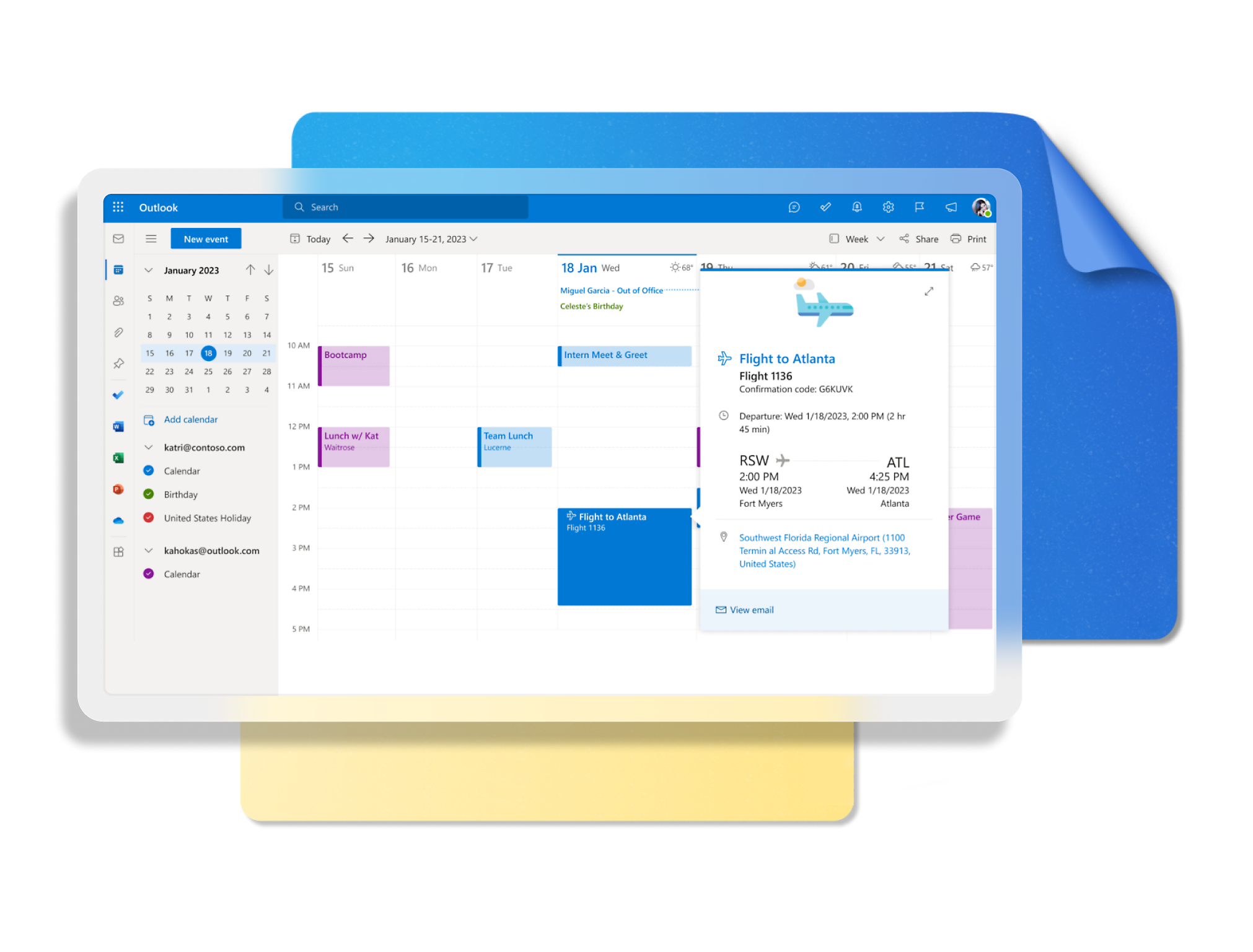
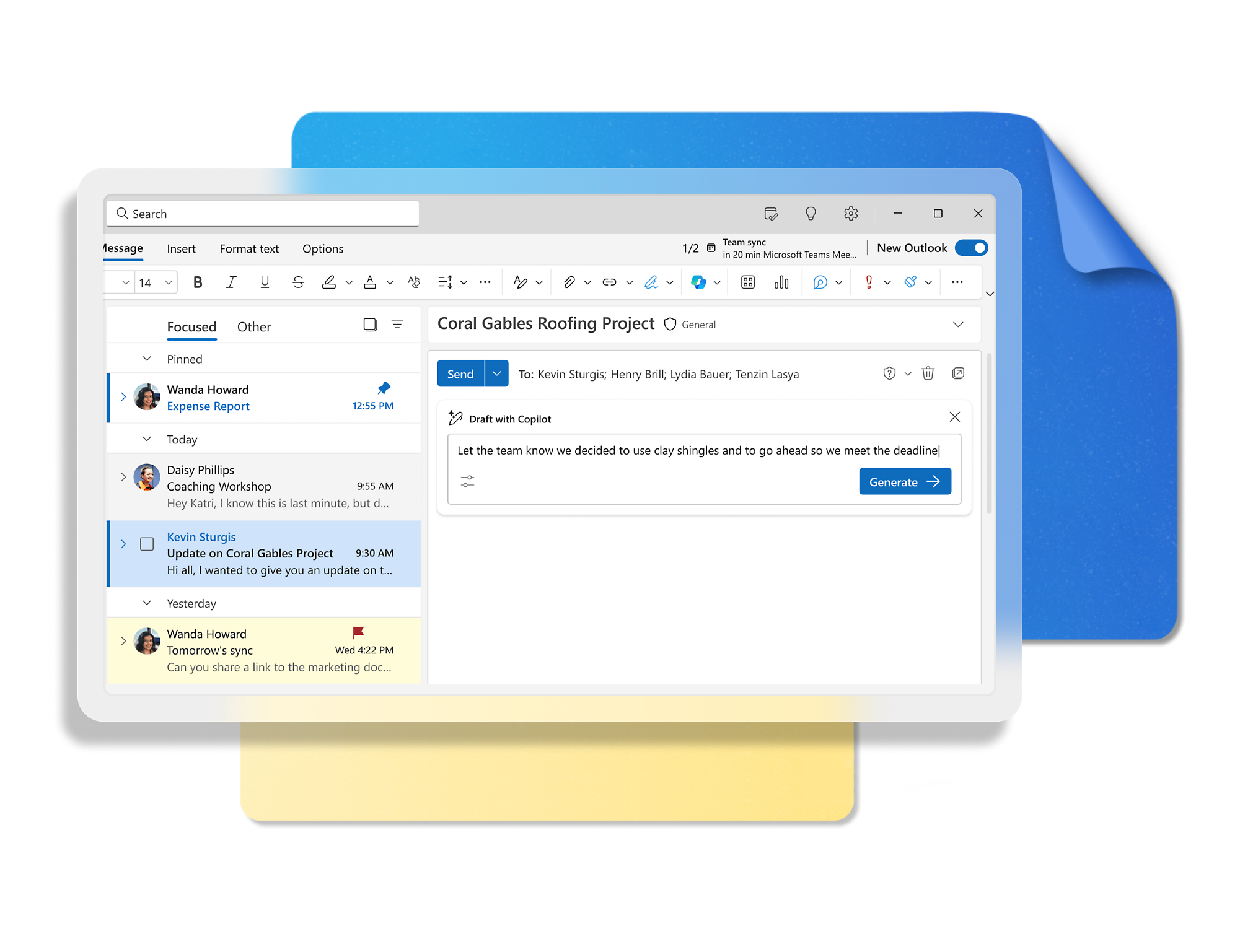
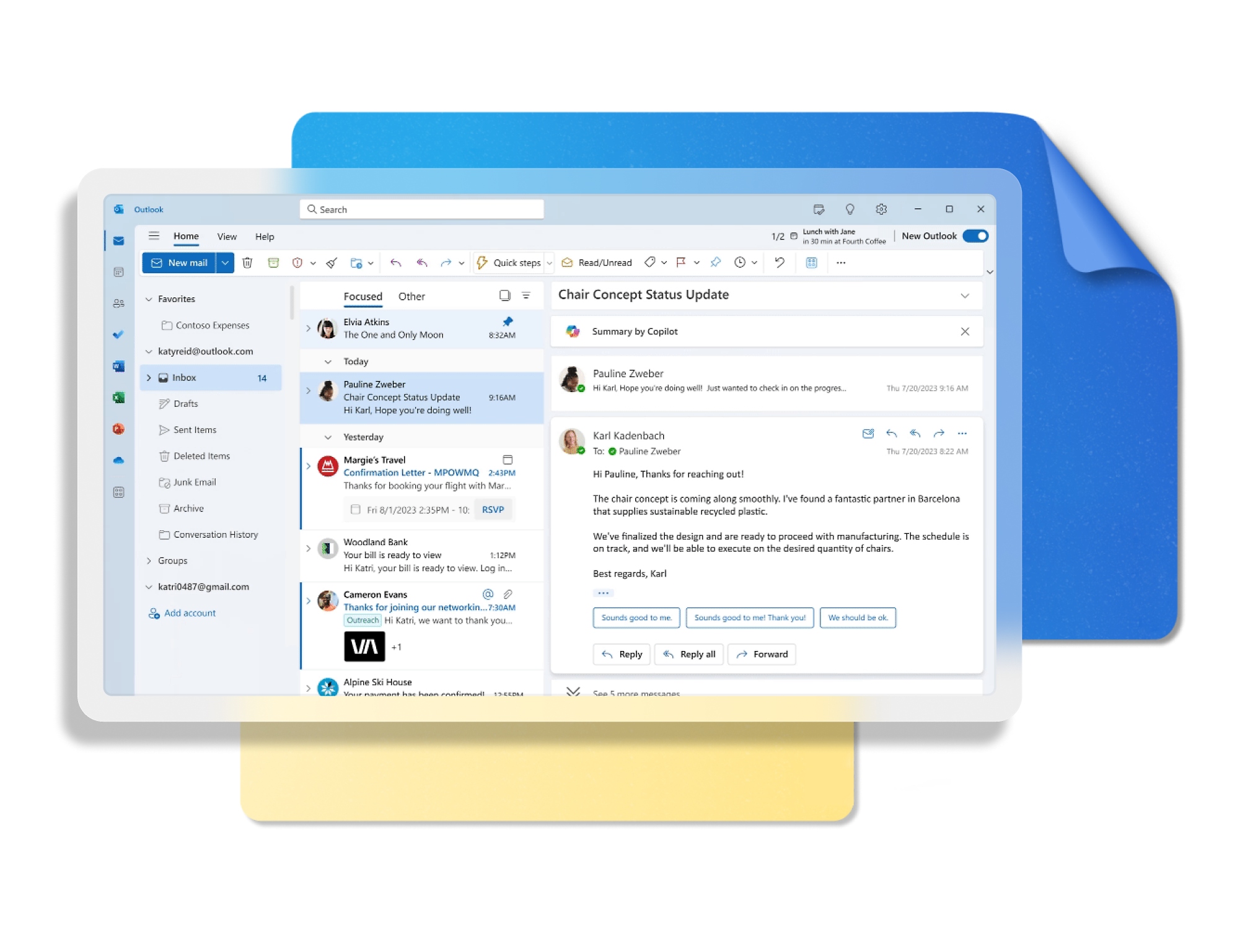
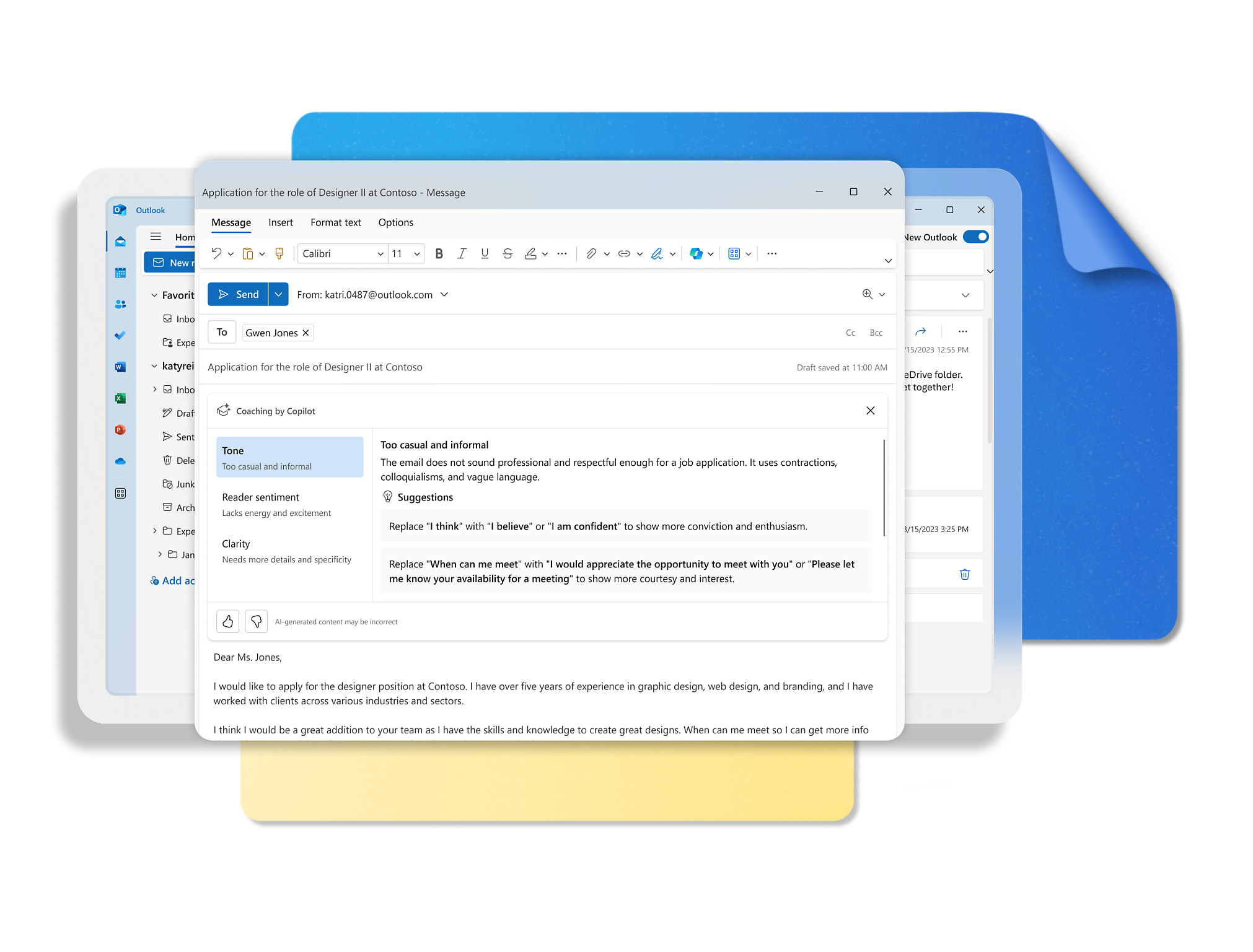
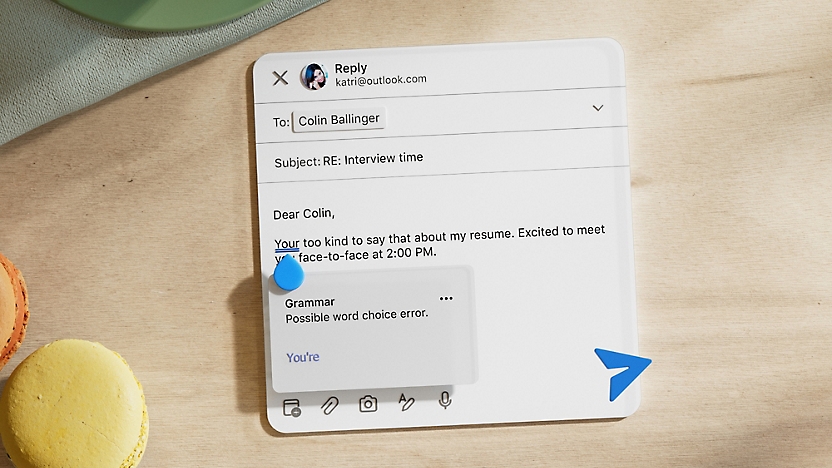
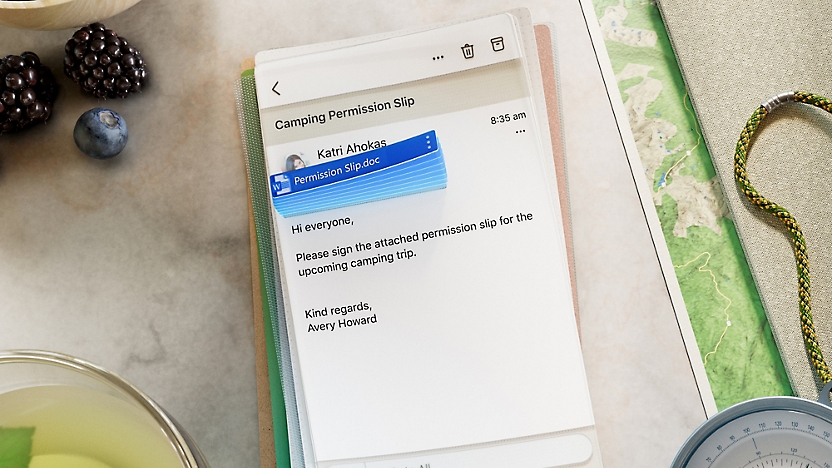
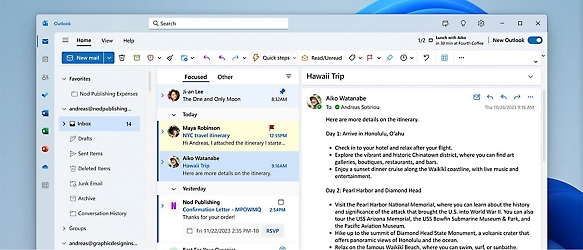
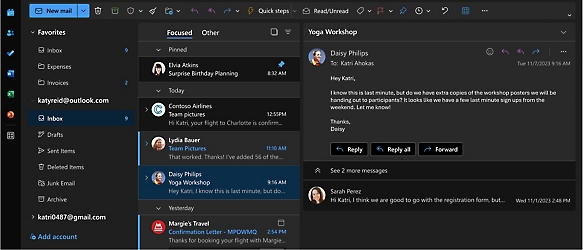
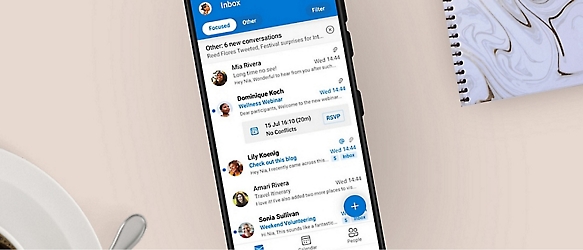
Manage what’s important with Outlook. Whether it’s different email accounts, multiple calendars, or signing that form, Outlook has you covered--whether at home or on the go.
Download the app
Outlook wherever you are

Plans & Pricing
Outlook is better with Microsoft 365
Microsoft 365 apps
Learn more about Microsoft 365 products
Partner Solutions
Apps for Microsoft 365
Work smarter in Outlook with apps tailored to help you communicate, manage your schedule, and find what you need—simply and fast.
Content is Loading...

News and tips
Get the latest on Microsoft Outlook
FAQ
- To create an Outlook.com account, you can click the “Create free account” button at the top of this site.
- Yes! You can use these accounts across all Outlook apps with the benefits that come with free or paid plans, depending on which you have.
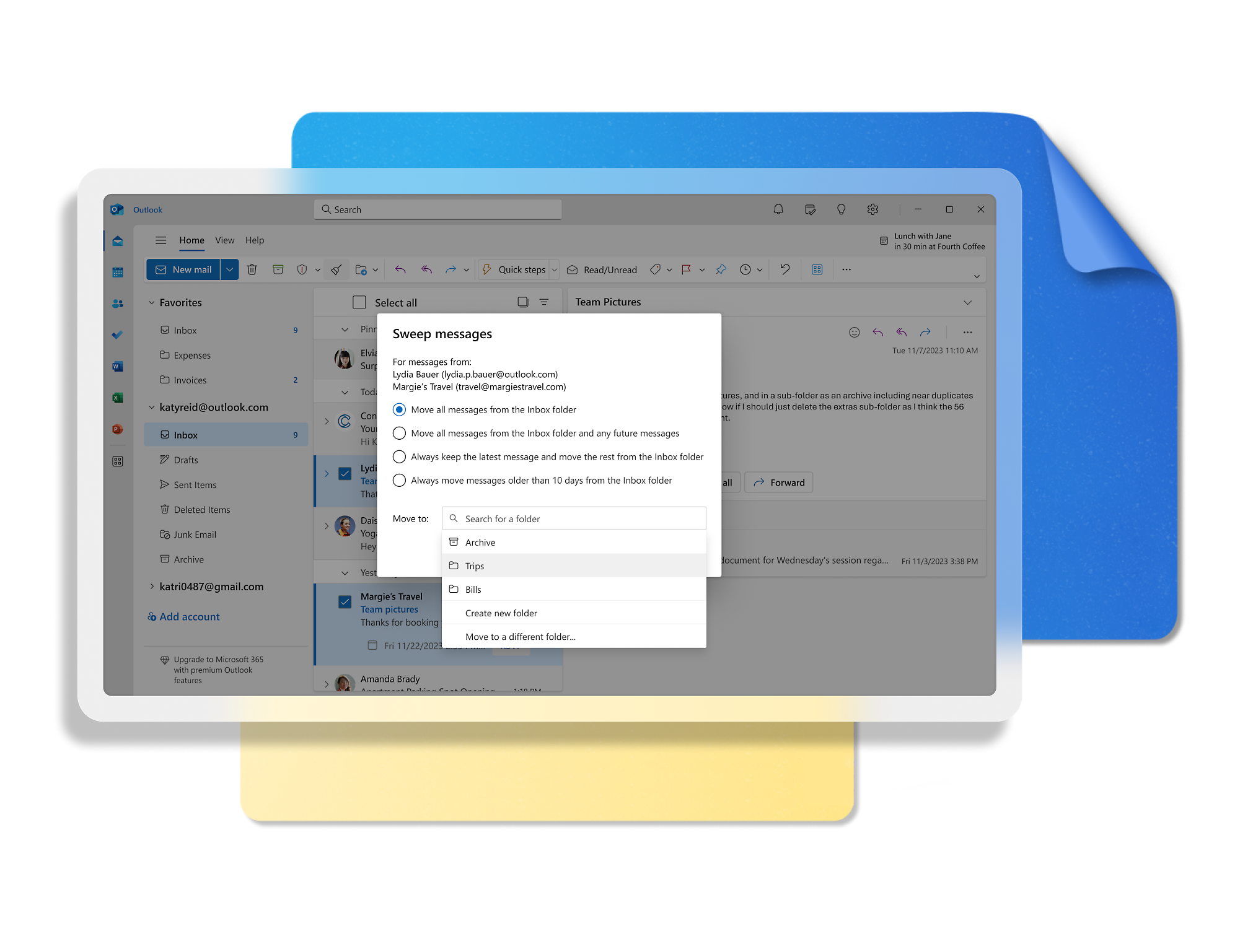
- Yes! Outlook desktop apps on Windows and Mac and mobile apps on iOS and Android support most third-party accounts including Gmail, Yahoo!, iCloud, and more. You can access multiple personal accounts as well as your work or school accounts all in a single Outlook app. This will help put all your mail and calendars in one place. Toggling between accounts is simple with a few clicks of a button, without leaving the app.
- For details on Outlook mailbox storage and Microsoft storage, please see this support article.
- If you have a paid account, you do not receive ads. This includes customers using Outlook with a Microsoft 365 account provided by their company, school, or organization. It also includes those who have a Microsoft 365 Basic, Personal, or Family subscription.
If you use a free email service such as Outlook.com, Hotmail, or Gmail without a Microsoft 365 subscription, you’ll see ads in your inbox clearly marked with an ad label to distinguish them from other emails. If you prefer not to see ads, you may purchase a Microsoft 365 subscription to remove any advertising served by Microsoft. Experiences for Microsoft 365 for Business and education subscribers may vary by plan. - Customers who have a Microsoft 365 Basic, Personal, or Family plan get an ad-free inbox, 100 GB of Outlook mailbox storage, and advanced security features2. They also receive data encryption in their mailbox and for the emails they send; automatic protection from suspicious links in emails; scans for viruses and malware; and removal of dangerous attachments.
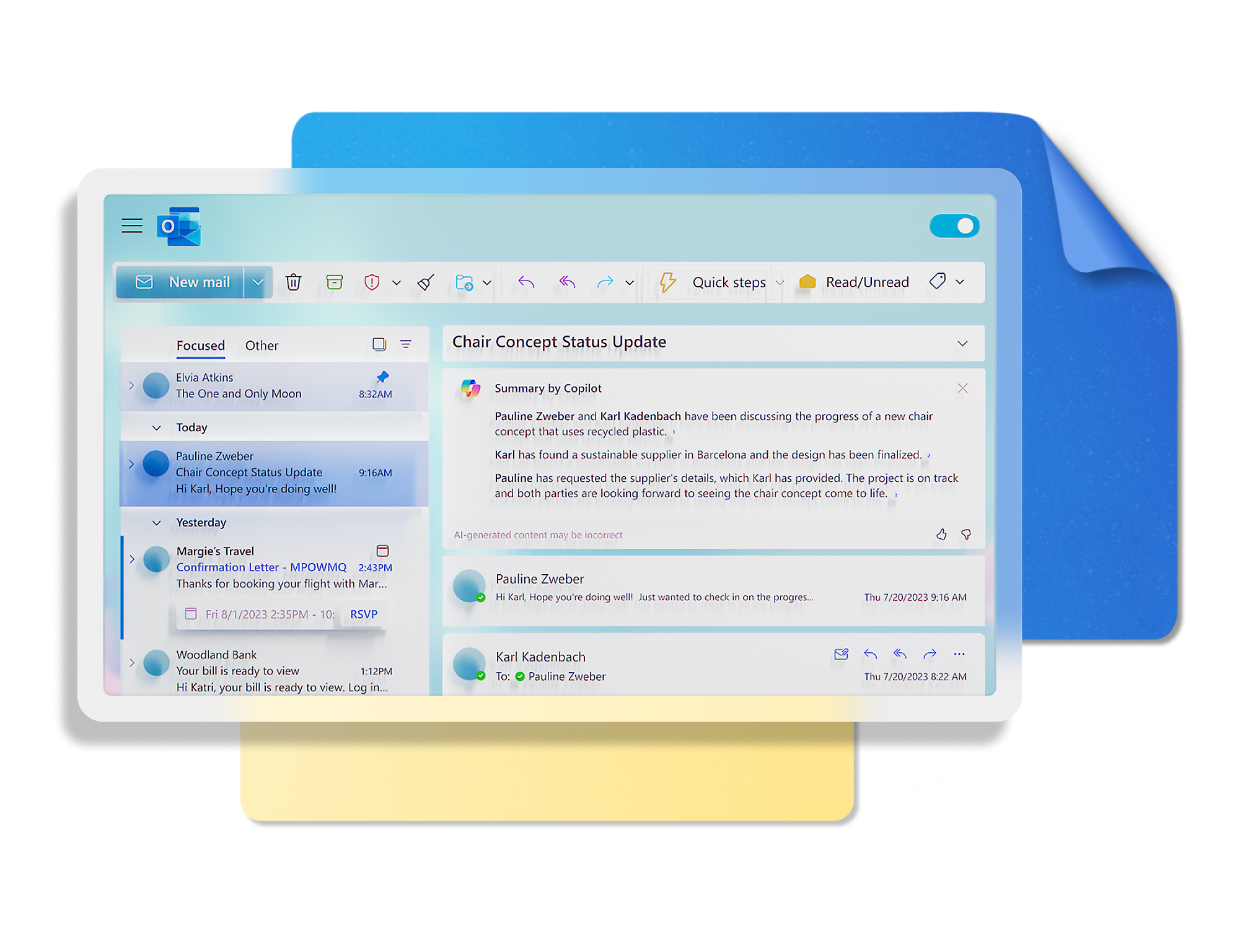
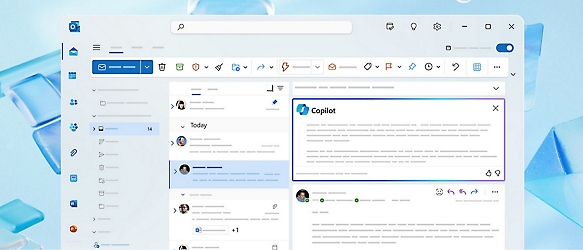
With a Personal or Family plan, you can additionally enjoy Copilot4 in Word, Excel,6 PowerPoint, OneNote, and Outlook, as well as premium Microsoft Editor functionality and advanced email management features like search folders, quick steps and conditional formatting. Personal and Family plans also offer offline and desktop access to Microsoft 365 apps such as Word, Excel, and PowerPoint, plus up to 6 TB secure cloud storage (1 TB per person) which covers OneDrive files and photos as well as Outlook email attachments.
Copilot in Outlook currently works with outlook.com, hotmail.com, live.com, and msn.com email addresses. - You’ll be asked to activate your Office license, which will enable access to all the productivity apps that come with your license, including ad-free classic Outlook for Windows (Win32) or Outlook for Mac.

Create free account
Don’t have an account? Get started with a free Outlook.com email today.
Try premium
Get the best Outlook experience with a Microsoft 365 subscription.
- [2]Features apply to customers who have an @outlook.com, @hotmail.com, @live.com, or @msn.com account. Copilot features are available in Outlook.com, Outlook built into Windows, Outlook on Mac, and iOS and Android apps.
- [3]Available with a Microsoft 365 subscription.
- [4]AI features only available to subscription owner and cannot be shared; usage limits apply. Learn more.
- [6]Copilot in Excel requires AutoSave to be enabled, meaning the file must be saved to OneDrive; it doesn't function with unsaved files.
- [7]Identity theft monitoring is only available in the United States and US territories.
- [8]After your one-month free trial, you will be charged the applicable subscription fee. A credit card is required. Cancel any time to stop future charges.
- [9]Once your paid subscription begins, cancelation policies vary based on your status as a new customer, product, and domain selections on Microsoft. Learn more. Cancel your Microsoft 365 subscription any time by going to the Microsoft 365 admin center. When a subscription is canceled, all associated data will be deleted. Learn more about data retention, deletion, and destruction in Microsoft 365.























Follow Microsoft 365